Tackling the causes of crime, not sending more people to jail, is the only way to fight it.

What ‘psychological warfare’ tactics do scammers use, and how can you protect yourself?

How economics can shed light on the motivations of extremist groups like Hamas.

How to protect your data privacy: A digital media expert provides steps you can take and explains why you can’t go it alone
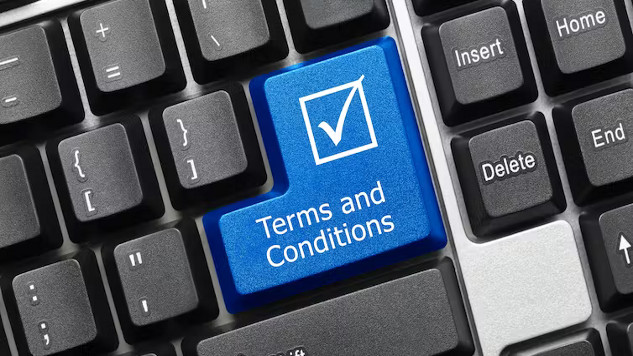
Dark patterns: how online companies strive to keep your money and data when you try to leave

When police get suspected drug abusers treatment rather than arresting them, those people are less likely to abuse drugs or commit drug-related crimes in the future, new, limited research finds.
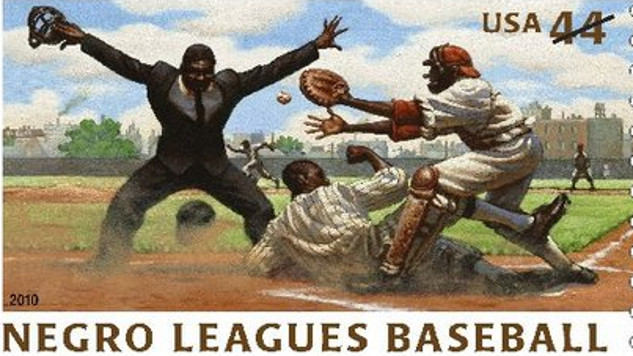
Baseball, often dubbed America's pastime, carries a rich and diverse history that has shaped the nation's identity.

The U.S. Federal Trade Commission (FTC) recently filed a complaint stating that, for years, Amazon has “knowingly duped” consumers into signing up for Prime subscriptions and then complicated their attempts to cancel.
- By Robbee Wedow

Many repositories store genetic data and other biospecimens like blood, urine or tumor tissue to be used in a wide number of future studies.

A series of gunshots fired late at night in East Atlanta recently prompted my neighbor to post on our local Facebook group, asking what we can do as a community to make it less dangerous to live and work in the area.

There has been a tenfold increase in sexual abuse imagery created with webcams and other recording devices worldwide since 2019, according to the the Internet Watch Foundation.

You have just returned home after a long day at work and are about to sit down for dinner when suddenly your phone starts buzzing. On the other end is a loved one, perhaps a parent, a child or a childhood friend, begging you to send them money immediately.

In exchange for access to their digital products and services, many tech companies collect and use our personal information. They use that information to predict and influence our future behaviour.
Keeping up with the latest digital cons is exhausting. Fraudsters always seem to be one step ahead.

The internet plays a central role in our lives. I — and many others my age — grew up alongside the development of social media and content platforms.

With nearly 84% of the world’s population now owning a smartphone, and our dependence on them growing all the time, these devices have become an attractive avenue for scammers.

Increased police monitoring of young people leads to more school discipline referrals and arrests, typically of Black and Latino youth.

When you use the internet, you leave behind a trail of data, a set of digital footprints. These include your social media activities, web browsing behavior, health information, travel patterns, location maps, information about your mobile device use, photos, audio and video.

Have you ever felt a creeping sensation that someone’s watching you? Then you turn around and you don’t see anything out of the ordinary. Depending on where you were, though, you might not have been completely imagining it.

Houses are getting smarter: smart thermostats manage our heating, while smart fridges can monitor our food consumption and help us order groceries. Some houses even have smart doorbells that tell us who is on our doorstep.

Many people think of privacy as a modern invention, an anomaly made possible by the rise of urbanization. If that were the case, then acquiescing to the current erosion of privacy might not be particularly alarming.

Scholars disagree about whether the formerly whites-only neighbourhoods of Johannesburg, South Africa’s largest and most economically important city, have become substantially desegregated since the end of apartheid in 1994

Pursuing master’s and doctoral degrees may help people improve their careers and help bring about changes in society, ranging from human rights protection, environmental conservation and gender equality to religious, racial and cultural solidarity.